LastPass patched three separate bugs that affected its Chrome and Firefox browser extensions, which if exploited, would have allowed a third-party to extract passwords from users visiting a malicious website.
All bugs were discovered by Tavis Ormandy, a security researcher working for Google's Project Zero.
One bug affected the LastPass for Chrome extension, while the other two affected the company's Firefox add-on.
Bug in LastPass Chrome extension
The vulnerability affecting the LastPass Chrome extension can be exploited by attacking an intermediary JS script that stands between the user's browser and the LastPass cloud service, where the company stores user passwords.
"It's possible to proxy untrusted messages to LastPass 4.1.42 due to a bug, allowing websites to access internal privileged RPCs (Remote Procedure Calls). " Ormandy explained. "There are a lot of RPCs, allowing complete control of the LastPass extension, including stealing passwords. If you have the 'Binary Component' installed, this even allows arbitrary code execution."
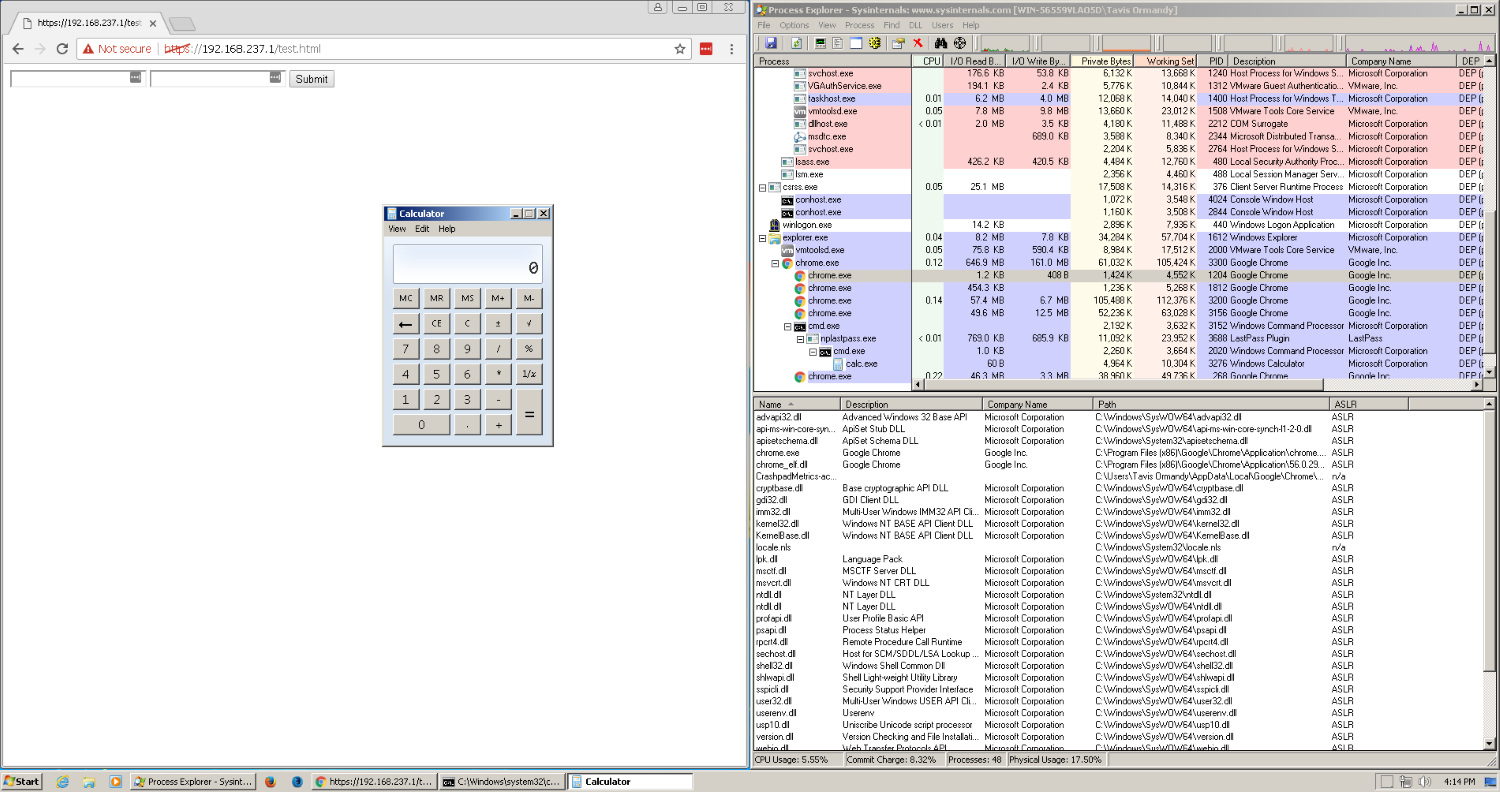
Ormandy put together proof-of-concept code that executes code on a user's machine via this intermediary script and launches an instance of the Windows Calculator. All OS platforms are affected, not just Chrome on Windows.
This PoC code can be altered to steal user passwords before they are copied and filled inside username and password fields.
LastPass users are exposed to simple attack vectors, as attackers can host the weaponized code as a regular JS script on a website.
On Twitter, LastPass said they already fixed the issue reported by Ormandy in the Chrome extension and later published a blog post with more details about all issues.
Bug in LastPass Firefox extension
The second and third bugs Ormandy discovered affect the LastPass Firefox add-on version 3.3.2 only. LastPass told Ormandy that version 3.3.2 is their most popular version.
Despite this, two weeks ago, LastPass announced they were retiring the LastPass Firefox add-on v3.3.2 because of Firefox's future plans to drop the old Add-ons API and move to a new system they call WebExtensions. The LastPass Chrome and Firefox extensions don't use the same version numbers, and the v3 on Firefox is the stable branch.
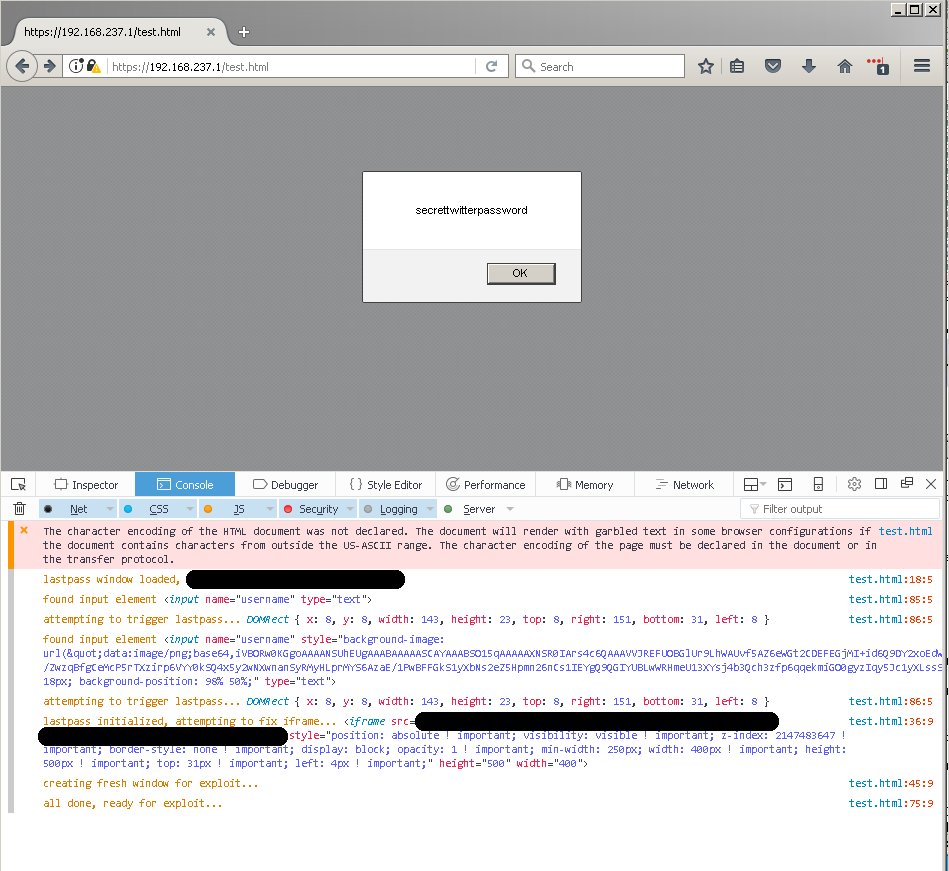
Just like the Chrome extension issue, the exploitation vector for these two issues is malicious JavaScript code that can be hidden in any online website, owned by the attacker or via a compromised legitimate site. Below is a screenshot of the second bug in action, while a demo page for the third issue is here.
In July 2016, Ormandy found a similar bug that allowed attackers to extract passwords from LastPass. On the same day, Mathias Karlsson of Detectify found and disclosed a different issue, wich also led to a full password compromise.
In April 2016, Malwarebytes found a fake LastPass Chrome extension offered via the official Google Web Store.
In January 2016, security researcher Sean Cassidy developed a simple attack to collect LastPass master passwords.
Any of these vulnerabilities should not keep users from installing a password manager, as this tweet wisely points out.
I worry people will read @taviso research on LastPass vulnerabilities as reasons not to use a password manager.Better than reusing passwords
— Jake Williams (@MalwareJake) March 22, 2017
Your odds of being pwned by a LastPass issue are far lower than if your password is disclosed from one site and reused on another. https://t.co/vKr6kXzL0F
— Jake Williams (@MalwareJake) March 22, 2017
UPDATE [March 22, 2017 17:15 ET]: Article updated with details about the third bug, and to reflect the fact that LastPass fixed all issues.


Comments
GT500 - 7 years ago
At least security researchers are finding vulnerabilities and reporting them so they can be fixed. I'd rather have that than the security vulnerabilities go unnoticed by the good guys, and the bad guys find them instead.