CISSP® – Certified Information Systems Security Professional Online Training | CISSP Training 2024 Latest Version
 Read Reviews
Read Reviews
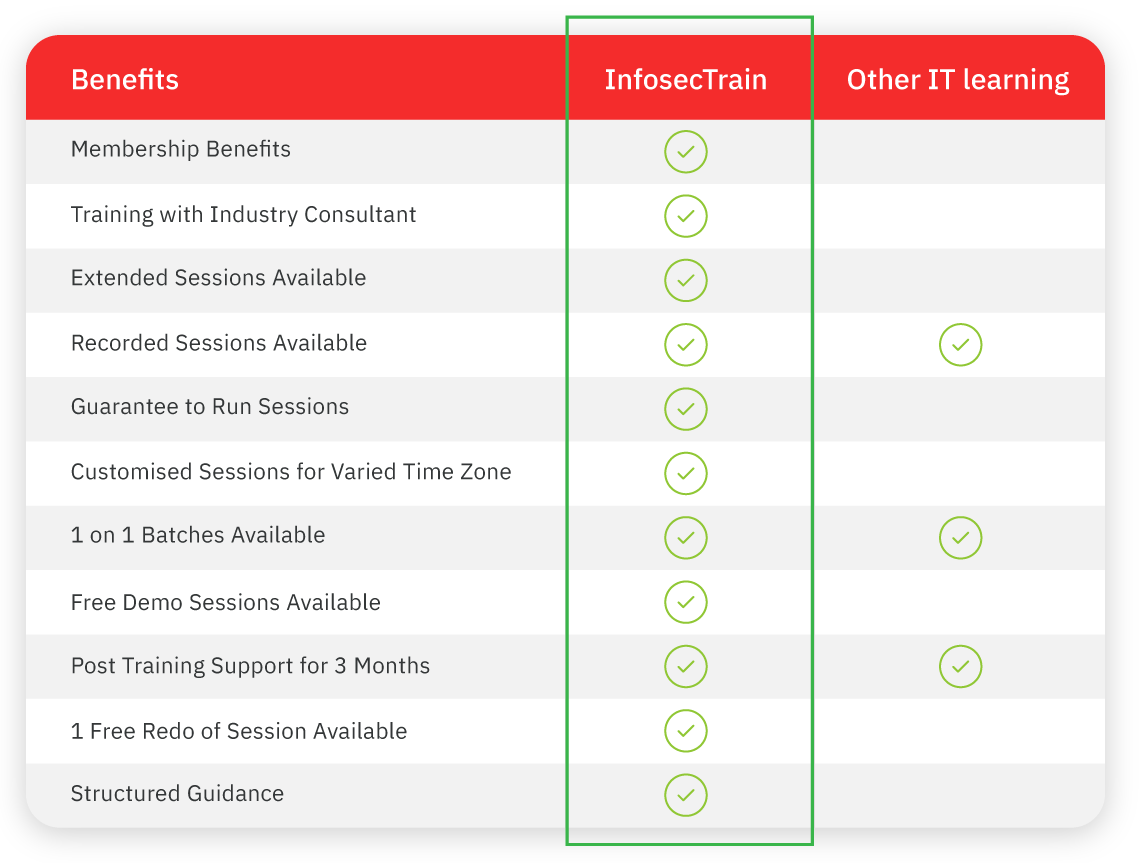
The Certified Information Systems Security Professional (CISSP®) certification training course offered by InfosecTrain is perfectly suited for individuals working in the field of information security. The latest version (2024) of CISSP enhances the participant’s understanding by covering the critical elements of the 8 domains that comprise the Common Body of Knowledge (CBK)®. This course aims to equip learners with both the technical and managerial competencies required to design, architect, and oversee an organization’s security framework in alignment with internationally accepted information security principles.





 5th Sep: Weekend
5th Sep: Weekend 









 It was great experience. Most of concepts were cleared in the course. The trainers are really good and engaging.
It was great experience. Most of concepts were cleared in the course. The trainers are really good and engaging.





 Certified & Experienced Instructors
Certified & Experienced Instructors Post Training Support
Post Training Support Customized Training
Customized Training Flexible Schedule
Flexible Schedule Access to Recorded Sessions
Access to Recorded Sessions 







 1800-843-7890 (India)
1800-843-7890 (India) 
