Professional Documents
Culture Documents
IJISRT20JAN621
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
IJISRT20JAN621
Copyright:
Available Formats
Volume 5, Issue 1, January – 2020 International Journal of Innovative Science and Research Technology
ISSN No:-2456-2165
Cryptosystems Using Algorithms,
Mechanism Techniques and Network
Privacy Management- A Survey
G. Avinash (1), B.Ashwin Meshak (2) , K.Gokul Prasath (3), R.Karthick Raja (4), U. Sarath (5)
Department of Electronics and Telecommunication Engineering
Karpagam College of Engineering, Coimbatore
Abstract:- With the advancement in technology, a need II. HACKING – A LITERATURE REVIEW
for secured data communication also arises which is
fulfilled by security mechanism techniques like data The term “Hacker” originally refers to someone who
integrity, digital signatures, Traffic Padding, Routing analysed computers deeply. Today, media recognised
Control, and access control. In various organizations, Hackers as “those who committed computer crimes”
enterprises and institutions, network privacy is involved [1].Two serious types of hackers include paid hackers and
and it is one of the major parameters. Confidentiality of underemployed hackers. Criminal hackers, students,
the information is a foremost thing for a concern. For security experts are the major categories in which a hacker
the protection of data and secured communication, this is likely to fall under. Ethical hacking is hired in large
paper aims at implementing several algorithms and internet service based corporations. Hacking trend is
mechanism techniques. increasing on a large basis particularly among the students.
Students enroll in computer-related courses. 80% of
I. INTRODUCTION hacking activity on the Internet is caused because of student
hackers. Using a computer network directly, Internet
The term cryptography refers to “secret writing”. connection, Remote control server are the major ways
Commonly termed as “Cipher-system”, Cryptography is a through which a hacker tries to access network. A series of
technique used to transform and transmit highly methods are used by hackers in order to target an attack.
confidential data or Information in an encoded way so that When the resources are infected with virus or malware
only authorized can obtain or work on it and illegal data significant data loss occurs along with the eradication of
accessing can be avoided. It is a Greek origin word in components of the network [6]. Through these virus
which “crypto” refers to hidden and “graphy” refers to activities, hard disks and processors gets destroyed and it
writing, so cryptography refers to hiding or secret writing. utilises large scale memory and slows down the system’s
Cryptography can also be referred to the “art and science of performance[9].
achieving security by encoding message to make them non-
readable which means it is used for privacy purpose”
.Cryptography introduces techniques such as
confidentiality, integrity and authenticity within on-going
data communication.
Two different types of cryptography exist. They are
symmetric key and asymmetric key cryptography. Plain
text, cipher text, encryption and decryption are the most
important key terms that deals a cryptosystem. Another
technique used in the data hiding is “Steganography”. In
Fig 1
this technique, hidden message is absent and original data
can’t be accessed. Steganography means cover writing.
Criminal hackers are those who have compromised
Steganography prevents secret information by creating the
internet services to steal credit or debit card numbers,
suspicion. Steganography refers to the practice of
aadhar card details and other details[1]. Recently,
communicating using hidden messages, often disguised
camscanner, a mobile application that allows Android
within something else where one would not expect a
devices to be used as image scanners has been hacked. On
message to be contained in. Various forms of
August 27, 2019, Russian security provider Kaspersky
steganography include text, audio, video, images.
Lab found that recent versions of the Android app
distributed an advertising library containing a Trojan
Dropper, which was also included in some apps preinstalled
on several Chinese mobiles and our personal data hacking.
The advertising library decrypts a Zip archive which
subsequently downloads additional files from serves
controlled by hackers, allowing the hackers controlling the
IJISRT20JAN621 www.ijisrt.com 800
Volume 5, Issue 1, January – 2020 International Journal of Innovative Science and Research Technology
ISSN No:-2456-2165
device [2]. Google ,an American based organization, as secret key cryptography [8]. In a public key
removed the application from the Google playstore. A new cryptosystem, different keys are used for encryption and
version of the application was launched by Google Play decryption process. In a public key encryption
Store on September 5, 2019. cryptosystem, major elements are involved are plain text,
encryption algorithm, decryption algorithm, public keys,
III. ANALYSIS OF ALGORITHMS TO private keys and cipher text. A plain text is an information
IMPLEMENT PRIVACY MANAGEMENT which is an input data and cipher text is the encrypted
message which is also the output[4]. Public and private
In general, a cryptographic system has two types of keys have been selected for encryption and decryption
keys namely secret key or private key and public key. process. The encryption process on the plaintext and
When the same key is used for both encryption and decryption process on the cipher text follows several
decryption such encryption, then that mechanism is known algorithms.
Fig 2
A. Diffie-Hellman Key Exchange: Implementing Rsa Algorithm:
Two users namely Alice and Bob have to agree
on p and q in private and they choose positive whole- STEP 1: GENERATION OF RSA MODULES:
number personal keys as a and b, both less than the prime- In the generation of RSA module, given two prime
number modulo p. Each side maintain ’a’ as private value numbers p and q, their product ‘N’ can be evaluated as
and ‘b’ as public value. Next, Alice and Bob figures out follows:
public keys a* and b* based on their personal keys N=p*q
according to the formulas: Here, we assume ‘N’ to be a specified large number.
a* = qa *mod p
and STEP 2: DERIVED INTEGER
b* = qb *mod p Here, we assume a number ‘e’ such that |e|>1 and it should
be less than (p-1) and (q-1). There should be no common
These two users share their public keys a* and b* over factor of (p-1) and (q-1) except 1(prime number).
a transmission medium assumed to be insecure, such as
the Internet. From these public keys, a number x can be STEP 3: GENERATION OF PUBLIC KEY
made to generate by either user on the basis of their own The two pair of numbers n and e forms the RSA public key
personal keys. To compute X, Alice uses the formula and it is made public.
x = (b*)a mod p
Bob computes x using the formula STEP 4: GENERATION OF PRIVATE KEY
x = (a*)b mod p To evaluate private key ‘d’ from the numbers p, q and e.
The mathematical relationship between the numbers is
The value of x turns out to be the same according any given by
of the above two formulas. Exchanging of secret value has M= (p-1)*(q-1);
been made. However, the personal keys a and b, which are e*d=1 mod(M);
critical in the calculation of x, have not been
transmitted/passed over a public medium. Because it is a Extended Euclidean Algorithm uses the same formula
large and apparently a random number, the two users can which takes p and q as the input parameters.
therefore, communicate privately over a public medium
with an encryption method of their choice using the Formula for Encryption:
decryption key x[4]. To encrypt the plain text message in the given
scenario , we have a sender who sends the plain text
B. RSA Algorithm: message to another user whose public key is (n,e). The
RSA stands for Rivest, Shamir and Adleman who syntax is:
discovered one of the most secured way of encryption. It C = (P*e) mod n
is a public key encryption technique. It is also named as
RSA algorithm[7]. RSA algorithm consists of two keys
namely a public key and a private key.
IJISRT20JAN621 www.ijisrt.com 801
Volume 5, Issue 1, January – 2020 International Journal of Innovative Science and Research Technology
ISSN No:-2456-2165
Formula for Decryption: C. Data Encryption Standard:
The decryption process includes analytics for The Data encryption standard(DES), the data blocks
calculation in a systematic approach[4]. Considering are encrypted in a 64-bit block with a 56-bit key[4]. In this
receiver C with private key d, the result modulus will be algorithm, transformation of 64-bit input to 64-bit output
calculated as – takes place. For reversing encryption, the same key is
Plaintext = Cd mod n followed. The inputs include a plain text to be encrypted
and the encryption key. The length of the plain text is 64-
bits and the key length is 56-bits.
Fig 3
The left and right halves of the output are D. Advanced Encryption Standard:
interchanged and pre-output is produced[4]. DES structure Advanced Encryption standard also known as AES
is similar to Feistal cipher. In the case of DES decryption, which is intended for replacing DES method of encryption.
the same technique which is used for data encryption It is a symmetric block cipher technique[4]. In AES, the
standard is followed with the keys reversed. block size of plaintext is 128-bits which is considered by
the cipher. The length of the key can be 16,24 ,32 bytes.
This can be referred to as AES-128, AES-192 or AES-256
algorithms which depends on the length of the key.
Fig 4
The input given to the encryption and decryption performed on data stored in an array is defined by AES
algorithm is always a 128-bit block. In the case of FIPS structure. In the first (N-1) rounds, four distinct functions
PUB, 4*4 square matrix of bits is the input considered. The occur. They are SubBytes, ShiftRows, MixColumns and
cipher consists of ‘N’ number of rounds and ‘N’ depends AddRoundKey[4]. In each transformation, there will be one
upon the key length. The number of transformations to be or more 4*4 matrix as input and 4*4 matrix as output.
IJISRT20JAN621 www.ijisrt.com 802
Volume 5, Issue 1, January – 2020 International Journal of Innovative Science and Research Technology
ISSN No:-2456-2165
E. Blowfish: received needs to be authenticated if it is sent by trusted
Blowfish algorithm uses cipher whose key varies sender[6]. It is the necessity of every organization and
within 32 to 448 bits of length. It’s features include institutions because it enables them to keep their networks
selection of secured way of message transformation[1]. secure by permitting only authenticated users to access its
protected resources. The resources covers computer
systems, databases, websites and other network-aided
applications. Authorization is another security mechanism
which gives permission to do or have something. It is used
to determine whether a person or system is allowed access
to resources, based on an access control policy. User
identity verification is performed using authorization.
System administrator’s duty includes assigning permission
levels covering all system and user resources. Physical
security describes measures to design and to deny the
unauthorized access of personnel resources and other
properties from damage. It protects these assets from
physical threats including theft, vandalism, fire and natural
Fig 5 disasters.
Linear and differential cryptosystems can be B. Integrity:
significantly analysed. It is available to both private as well Maintaining and assuring the accuracy and
as public sectors. It is a feistel network and it can be consistency of data is a way to achieve integrity of data.
inverted simply performing XOR with blocks P17 and P18 The data received by the recipient must be exactly same as
to the ciphertext block. the data sent from the sender, without change in even one
bit of data. The elements of integrity include backups,
IV. TECHNIQUES TO ACHIEVE A SECURED checksums and data correcting codes. Backup includes
SYSTEM archiving of data periodically. It is a process of making
duplicate copies of data to use it in the event when the
A most significant component in information security original data or data files are eradicated. It is mainly used to
is network security management. Network security consists make copies for historical purposes, such as for
of underlying computer network infrastructure, policies longitudinal studies to meet the requirements of a data
adopted by the network administrator in order to protect the retention policy. A checksum is a numerical value that is
network and its resources from unauthorized access, and generated by the data in a process to verify the integrity of
continuous monitoring of the information. In the modern a file. A checksum function entirely relies on the entire
digital technology, organizations highly rely on computer contents of a file. It is a method for storing data in such a
networks to share the data throughout the organization in an way that small changes can be easily detected and
efficient and productive manner. Confidentiality, Integrity, automatically corrected.
availability are the three major elements that contribute to a
secured system which is represented by a CIA triangle[3]. C. Availability:
The term "Availability" in network Security is to
ensure that the resources (data) are available to the
legitimate users, whenever they require it. Availability
ensures timely and reliable access to use the
data[4].Physical safeguard and computational redundancies
are the major elements in the availability of data. Physical
safeguard is to keep information available even in the event
of physical challenges. It ensure sensitive information is
housed in secure areas.
Security services are provided by a protocol layer of
communicating open systems to ensure adequate security of
the systems or of data transfer[4]. This falls under X.800.
Fig 6 Also the RFC 2828 defines security services as a
communication service that is provided by a system to give
A. Confidentiality: a specific kind of security to system resources. Security
Confidentiality element of a network Security makes Services can be implemented by security policy and
sure that the data is available only authorized persons The mechanisms techniques.
components of confidentiality include data encryption,
access control, authentication, authorization and physical
security. An authentication is a mechanism that ensures and
confirms a user's unique identity that someone has. All data
IJISRT20JAN621 www.ijisrt.com 803
Volume 5, Issue 1, January – 2020 International Journal of Innovative Science and Research Technology
ISSN No:-2456-2165
Encipherment: Notarization:
It involves hiding and covering the data to achieve Notarization mechanisms allows establishing a third
confidentiality. Traffic flow information is provided by party to control communication between two or more
encipherment technique to support other security entities, such as its integrity. With the third party
mechanisms. establishment, repudiation is prevented[5]. This is done to
store the sender’s request and delaying is reduced.
Data Integrity:
Data integrity technique consists of a short checkvalue V. CONCLUSION
which is generated by the data during a particular process.
At the receiving end, the receiver gets the data and the Privacy management is the most important element in
checkvalue. Receiver creates a new checkvalue from the cryptography Techniques. This paper significantly
received data and compares the new checkvalue and the examined several private and public key encryption
received checkvalue. If the two checkvalues matches, data techniques such as AES, DES, Blowfish, Diffie-Hellman
integrity is ensured. ,RSA. Information security has become significant. Several
algorithms have been evaluated and discussed. One can
Digital Signature: maintain privacy for his data using different security
A digital signature is a technique through which mechanism techniques like Cryptography, encipherment,
sender electronically signs the data and the receiver verifies data integrity, digital signatures, authentication exchange,
the signature in an electronic way. Public key and private firewalls, access controls and steganography. Essential
key relationships are ensured and both the sender and the mechanism techniques have been discussed to safeguard
receiver prove their identities to each other. In other words, our personal data.
a digital signature ensures whether an electronic document
is authentic or not. Digital signatures rely upon certain REFERENCES
types of encryption process to ensure authentication. In
encryption, all the data that one computer is sending to [1]. Firewalls by Matthew Strebe, Charles Perkins.
another is taken and encoded it into a form that only the [2]. https://en.wikipedia.org/wiki/CamScanner.
other computer will be able to decode. Authentication is the [3]. https://www.javatpoint.com/cyber-security-goals.
process of verifying that information is coming from a [4]. Cryptography and Network security by William
trusted source[4]. Stallings.
[5]. Cryptography and Network Security by Behrouz
Authentication Exchange: A.Forouzan.
In this method, two users exchange key with each [6]. Anu, Divya Shree and Seema Ahlawat, “ A review on
other to ensure their identities to each other[5]. Each user Cryptography, Attacks and Cyber Security”,
must have their unique usernames and secret key so that IJARCS,Volume.8, No.5, May-June 2017.
authorized persons can use it [6]. [7]. Neha Sharma, Prabhjot and Er.Harpreet kaur, “ A
review on Information Security using Cryptography
Access Control: technique”, IJARCS, Volume.8, No.4, May 2017.
Access control uses mechanisms to prove that a user [8]. A. Joseph Amalraj1, Dr. J. John Raybin Jose2, “ A
has the right to use identities, information of principals[5]. survey paper on Cryptography techniques”, IJCSMC,
If a mechanism attempts to use an unauthorized resource, Volume.5, Issue.8,August 2016,pp.55-59.
the access control function ignores the attempt and reports [9]. Rajesh R Mane,” A review on Cryptography
this incident to produce alarm and recording it. Algorithms, Attacks and Encryption Tools”,IJIRCCE,
Volume.3, Issue-9, September 2015.
Traffic Padding: [10]. https://www.webopedia.com/TERM/R/route_control.
Traffic padding mechanisms are used in order to html
safeguard from heavy traffic analysis and its attacks.
Traffic padding refers to the generation of bogus data and
data units to reduce traffic congestion[5].
Routing Control:
Routing control involves continuously monitoring the
route to establish the shortest path between the sender and
the receiver to provide communication. The information
which is carried on certain security labels may be restricted
by a security policy to pass through certain links. Handling
the switching policy of outgoing data between ISPs in real
time and its evaluation can be analysed using routing
control[10].
IJISRT20JAN621 www.ijisrt.com 804
You might also like
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Information Systems Security and ControlDocument10 pagesInformation Systems Security and ControlPraise NehumambiNo ratings yet
- Application Form For Registration of Professional DevelopersDocument11 pagesApplication Form For Registration of Professional DevelopersDINESH100% (5)
- Automatic Pistol Neuhausen SP 47-8 (Sig P210) ManualDocument13 pagesAutomatic Pistol Neuhausen SP 47-8 (Sig P210) ManualMichael ZelenyNo ratings yet
- S257a s40 Requirement To Provide BiometricsDocument4 pagesS257a s40 Requirement To Provide BiometricsBiraj ShresthaNo ratings yet
- Huawei CBS V500R005 Security Technical White PaperDocument36 pagesHuawei CBS V500R005 Security Technical White PaperChakravarthi Chittajallu67% (3)
- Advancing Healthcare Predictions: Harnessing Machine Learning for Accurate Health Index PrognosisDocument8 pagesAdvancing Healthcare Predictions: Harnessing Machine Learning for Accurate Health Index PrognosisInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Diabetic Retinopathy Stage Detection Using CNN and Inception V3Document9 pagesDiabetic Retinopathy Stage Detection Using CNN and Inception V3International Journal of Innovative Science and Research TechnologyNo ratings yet
- Comparatively Design and Analyze Elevated Rectangular Water Reservoir with and without Bracing for Different Stagging HeightDocument4 pagesComparatively Design and Analyze Elevated Rectangular Water Reservoir with and without Bracing for Different Stagging HeightInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Design, Development and Evaluation of Methi-Shikakai Herbal ShampooDocument8 pagesDesign, Development and Evaluation of Methi-Shikakai Herbal ShampooInternational Journal of Innovative Science and Research Technology100% (3)
- Terracing as an Old-Style Scheme of Soil Water Preservation in Djingliya-Mandara Mountains- CameroonDocument14 pagesTerracing as an Old-Style Scheme of Soil Water Preservation in Djingliya-Mandara Mountains- CameroonInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Cyberbullying: Legal and Ethical Implications, Challenges and Opportunities for Policy DevelopmentDocument7 pagesCyberbullying: Legal and Ethical Implications, Challenges and Opportunities for Policy DevelopmentInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- The Impact of Digital Marketing Dimensions on Customer SatisfactionDocument6 pagesThe Impact of Digital Marketing Dimensions on Customer SatisfactionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- The Utilization of Date Palm (Phoenix dactylifera) Leaf Fiber as a Main Component in Making an Improvised Water FilterDocument11 pagesThe Utilization of Date Palm (Phoenix dactylifera) Leaf Fiber as a Main Component in Making an Improvised Water FilterInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Dense Wavelength Division Multiplexing (DWDM) in IT Networks: A Leap Beyond Synchronous Digital Hierarchy (SDH)Document2 pagesDense Wavelength Division Multiplexing (DWDM) in IT Networks: A Leap Beyond Synchronous Digital Hierarchy (SDH)International Journal of Innovative Science and Research TechnologyNo ratings yet
- Formulation and Evaluation of Poly Herbal Body ScrubDocument6 pagesFormulation and Evaluation of Poly Herbal Body ScrubInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Auto Encoder Driven Hybrid Pipelines for Image Deblurring using NAFNETDocument6 pagesAuto Encoder Driven Hybrid Pipelines for Image Deblurring using NAFNETInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Electro-Optics Properties of Intact Cocoa Beans based on Near Infrared TechnologyDocument7 pagesElectro-Optics Properties of Intact Cocoa Beans based on Near Infrared TechnologyInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Explorning the Role of Machine Learning in Enhancing Cloud SecurityDocument5 pagesExplorning the Role of Machine Learning in Enhancing Cloud SecurityInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- A Survey of the Plastic Waste used in Paving BlocksDocument4 pagesA Survey of the Plastic Waste used in Paving BlocksInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- A Review: Pink Eye Outbreak in IndiaDocument3 pagesA Review: Pink Eye Outbreak in IndiaInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Navigating Digitalization: AHP Insights for SMEs' Strategic TransformationDocument11 pagesNavigating Digitalization: AHP Insights for SMEs' Strategic TransformationInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Automatic Power Factor ControllerDocument4 pagesAutomatic Power Factor ControllerInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Hepatic Portovenous Gas in a Young MaleDocument2 pagesHepatic Portovenous Gas in a Young MaleInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Studying the Situation and Proposing Some Basic Solutions to Improve Psychological Harmony Between Managerial Staff and Students of Medical Universities in Hanoi AreaDocument5 pagesStudying the Situation and Proposing Some Basic Solutions to Improve Psychological Harmony Between Managerial Staff and Students of Medical Universities in Hanoi AreaInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Review of Biomechanics in Footwear Design and Development: An Exploration of Key Concepts and InnovationsDocument5 pagesReview of Biomechanics in Footwear Design and Development: An Exploration of Key Concepts and InnovationsInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- The Effect of Time Variables as Predictors of Senior Secondary School Students' Mathematical Performance Department of Mathematics Education Freetown PolytechnicDocument7 pagesThe Effect of Time Variables as Predictors of Senior Secondary School Students' Mathematical Performance Department of Mathematics Education Freetown PolytechnicInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Mobile Distractions among Adolescents: Impact on Learning in the Aftermath of COVID-19 in IndiaDocument2 pagesMobile Distractions among Adolescents: Impact on Learning in the Aftermath of COVID-19 in IndiaInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Enhancing the Strength of Concrete by Using Human Hairs as a FiberDocument3 pagesEnhancing the Strength of Concrete by Using Human Hairs as a FiberInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Drug Dosage Control System Using Reinforcement LearningDocument8 pagesDrug Dosage Control System Using Reinforcement LearningInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Securing Document Exchange with Blockchain Technology: A New Paradigm for Information SharingDocument4 pagesSecuring Document Exchange with Blockchain Technology: A New Paradigm for Information SharingInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Intelligent Engines: Revolutionizing Manufacturing and Supply Chains with AIDocument14 pagesIntelligent Engines: Revolutionizing Manufacturing and Supply Chains with AIInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Formation of New Technology in Automated Highway System in Peripheral HighwayDocument6 pagesFormation of New Technology in Automated Highway System in Peripheral HighwayInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Perceived Impact of Active Pedagogy in Medical Students' Learning at the Faculty of Medicine and Pharmacy of CasablancaDocument5 pagesPerceived Impact of Active Pedagogy in Medical Students' Learning at the Faculty of Medicine and Pharmacy of CasablancaInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Supply Chain 5.0: A Comprehensive Literature Review on Implications, Applications and ChallengesDocument11 pagesSupply Chain 5.0: A Comprehensive Literature Review on Implications, Applications and ChallengesInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- The Making of Self-Disposing Contactless Motion-Activated Trash Bin Using Ultrasonic SensorsDocument7 pagesThe Making of Self-Disposing Contactless Motion-Activated Trash Bin Using Ultrasonic SensorsInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- ValidationRules & Input MaskDocument4 pagesValidationRules & Input MaskHerman OduorNo ratings yet
- WSC2017 TP39 ModuleB Actual PDFDocument17 pagesWSC2017 TP39 ModuleB Actual PDFJesus PradaNo ratings yet
- Microsoft CISO Workshop: 3 - Identity and Zero Trust User AccessDocument26 pagesMicrosoft CISO Workshop: 3 - Identity and Zero Trust User AccessKaito LeeNo ratings yet
- Fax B - KM2030 - U Error CodesDocument10 pagesFax B - KM2030 - U Error CodesmohamedcopiersNo ratings yet
- 76 MM GunDocument50 pages76 MM GunKidus Yado GirmaNo ratings yet
- Sangfor IAM V11.9 Associate 07 FirewallDocument19 pagesSangfor IAM V11.9 Associate 07 FirewallRandi AdipratamaNo ratings yet
- PNB C@shNet Plus User Enrollment FormDocument1 pagePNB C@shNet Plus User Enrollment FormRosie HepburnNo ratings yet
- Alex Michaelides Pacienta Tăcută PDFDocument358 pagesAlex Michaelides Pacienta Tăcută PDFPopa OanaNo ratings yet
- Database Security and AuthorizationDocument29 pagesDatabase Security and AuthorizationRoha CbcNo ratings yet
- Account Statement From 2 Jun 2020 To 2 Dec 2020: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument11 pagesAccount Statement From 2 Jun 2020 To 2 Dec 2020: TXN Date Value Date Description Ref No./Cheque No. Debit Credit Balanceanitha anuNo ratings yet
- Access Token Stealing On WindowsDocument11 pagesAccess Token Stealing On Windows@4e4enNo ratings yet
- Wu Install DocumentationDocument42 pagesWu Install DocumentationBenj AgravanteNo ratings yet
- Security Container Information Container Number Instructions CombinationDocument1 pageSecurity Container Information Container Number Instructions CombinationDoctor MotrinNo ratings yet
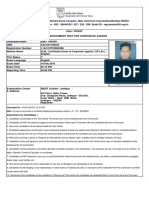
- Exam Hall Ticket for Corporate Agents TestDocument1 pageExam Hall Ticket for Corporate Agents Testamit tiwariNo ratings yet
- CCB2011 Information Brochure 09-06-2011 FINAL VersionIDocument98 pagesCCB2011 Information Brochure 09-06-2011 FINAL VersionIanon_315434879No ratings yet
- ch03 ProgramSecurity 2fDocument46 pagesch03 ProgramSecurity 2fPankaj SoniNo ratings yet
- CHAPTER 5: Control Frameworks 1. What Are The Five Components of The COSO IC-IF Model?Document5 pagesCHAPTER 5: Control Frameworks 1. What Are The Five Components of The COSO IC-IF Model?Marco RegunayanNo ratings yet
- ReportDocument29 pagesReportPritoj SinghNo ratings yet
- Mitsubishi Lancer Owners HandbookDocument194 pagesMitsubishi Lancer Owners Handbookahmadkeshta100% (1)
- Av Delphi LibDocument29 pagesAv Delphi Lib2912882No ratings yet
- Terms of Reference (Tor) and Guideline For Vendor Enlistment 2018-2019Document6 pagesTerms of Reference (Tor) and Guideline For Vendor Enlistment 2018-2019shoyebNo ratings yet
- Sciencedirect: Fuzzy Logic Based Image Encryption For Confidential Data Transfer Using (2, 2) Secret Sharing SchemeDocument8 pagesSciencedirect: Fuzzy Logic Based Image Encryption For Confidential Data Transfer Using (2, 2) Secret Sharing SchemeIsrarAhmadMarwatNo ratings yet
- Account Statement From 1 Apr 2021 To 19 Jun 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument9 pagesAccount Statement From 1 Apr 2021 To 19 Jun 2021: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceNrusingha Prasad MishraNo ratings yet
- Vibration Monitoring and Risk Analysis System For Process Piping - Case Study 613Document4 pagesVibration Monitoring and Risk Analysis System For Process Piping - Case Study 613vellore2kNo ratings yet
- 10c - Crime-Mapping in The PNP.. 3b-Case study-PNP Crime Mapping-2015Document11 pages10c - Crime-Mapping in The PNP.. 3b-Case study-PNP Crime Mapping-2015Gesler Pilvan SainNo ratings yet